
If you run a small business, there is a good chance you already have some kind of antivirus installed on your computers. That is a smart place to start, but it is no longer the full answer.
A lot of business owners still ask the same question: Is antivirus enough for a small business in 2026?
The honest answer is no. Antivirus still matters, but on its own it is not enough to protect a modern business from the types of threats causing the most damage today. Small businesses are dealing with far more than old-school viruses. The real risks now include phishing, ransomware, weak passwords, account takeovers, employee mistakes, unpatched software, cloud misconfigurations, and backup failures. Federal small-business guidance from both CISA and the SBA stresses layered protection like multi-factor authentication, software updates, employee training, backups, and secure networks, not just antivirus alone. Verizon’s 2025 DBIR also says small and medium businesses are being targeted nearly four times more than large organizations.
For many small businesses, the bigger issue is not whether antivirus is bad. It is whether it gives a false sense of security.
At Zevonix, we work with businesses that want practical, smarter IT. That means building protection that helps reduce risk, improve response times, and keep operations moving when something goes wrong. In this article, we will break down what antivirus actually does, where it falls short, and what a small business really needs in 2026.
Is Antivirus Enough for a Small Business in 2026? – Table of Contents
What antivirus does well
Antivirus still plays an important role in business security.
At its core, antivirus is designed to detect and block known malicious software. That includes traditional viruses, trojans, worms, and some forms of spyware or malicious downloads. Most modern antivirus tools can also flag suspicious files, monitor basic behavior, and quarantine threats before they spread.
That is useful. Every business should still have endpoint protection in place. The SBA even continues to recommend antivirus software as part of basic small-business cybersecurity hygiene, along with keeping software updated.
In simple terms, antivirus helps with:
- known malware
- infected file downloads
- some malicious attachments
- basic device-level threat detection
- some web and email threat filtering, depending on the product
So the answer is not that antivirus is outdated or pointless. The answer is that antivirus is only one layer.
Why antivirus alone is not enough in 2026
The biggest threats hitting small businesses today often do not start with a classic virus.
Many attacks begin with a fake login page, a compromised Microsoft 365 account, a phishing email, a stolen password, an unpatched firewall, or an employee clicking the wrong link. Some of the most damaging incidents happen because attackers get access using real credentials, then move through cloud apps, email, file sharing, and business systems. That kind of access can bypass the narrow idea of “virus protection.” CISA’s ransomware guidance emphasizes phishing resistance, patching, incident response planning, and tested backups because ransomware attacks often rely on much more than one malicious file landing on a PC.
This is where many business owners get caught off guard.
They think:
“We have antivirus, so we should be fine.”
But what happens if:
- an employee gives up their password to a fake Microsoft sign-in page?
- a hacker logs into email from another country using stolen credentials?
- your backups have not been tested and fail during recovery?
- an old device or network appliance has not been patched?
- a staff member installs an unapproved app that exposes company data?
- a ransomware attacker gets in through remote access or a vulnerable system?
Antivirus alone does not solve those problems.
The modern threats small businesses are actually facing
To understand why antivirus is not enough, it helps to look at the real threat landscape.
Phishing and social engineering
Phishing is still one of the easiest ways attackers get into a business. A fake invoice, fake Microsoft 365 alert, fake Dropbox message, or fake shipping notification can fool even smart employees if they are busy. The SBA specifically warns that employees are a leading cause of breaches and should be trained to spot suspicious files, phishing emails, and unsafe behavior.
Ransomware
Ransomware remains one of the biggest business killers because it can stop operations fast. It is not just about encrypted files anymore. Attackers often steal data, threaten exposure, and disrupt business continuity. CISA’s updated StopRansomware guidance continues to emphasize cloud backups, zero trust concepts, vulnerability remediation, and recovery preparation because prevention alone is not enough. Verizon’s SMB materials also highlight ransomware as a major concern for smaller organizations.
Credential theft and account compromise
If a criminal logs into your email, cloud storage, CRM, or accounting platform using a real username and password, your antivirus may not see that as a virus at all. That is why MFA, conditional access, strong password controls, and identity monitoring matter so much.
Unpatched systems and software
The SBA recommends automatic updates for operating systems, browsers, and applications because out-of-date systems create security gaps. CISA advisories continue to stress prompt patching as one of the most important security actions businesses can take.
Downtime and operational disruption
Even if a business avoids a full-scale breach, technical problems still cost time, money, and productivity. The U.S. Chamber’s current small-business IT management guidance points to support, account management, troubleshooting, and security as core needs because unresolved tech issues directly affect daily work.
What a small business needs beyond antivirus
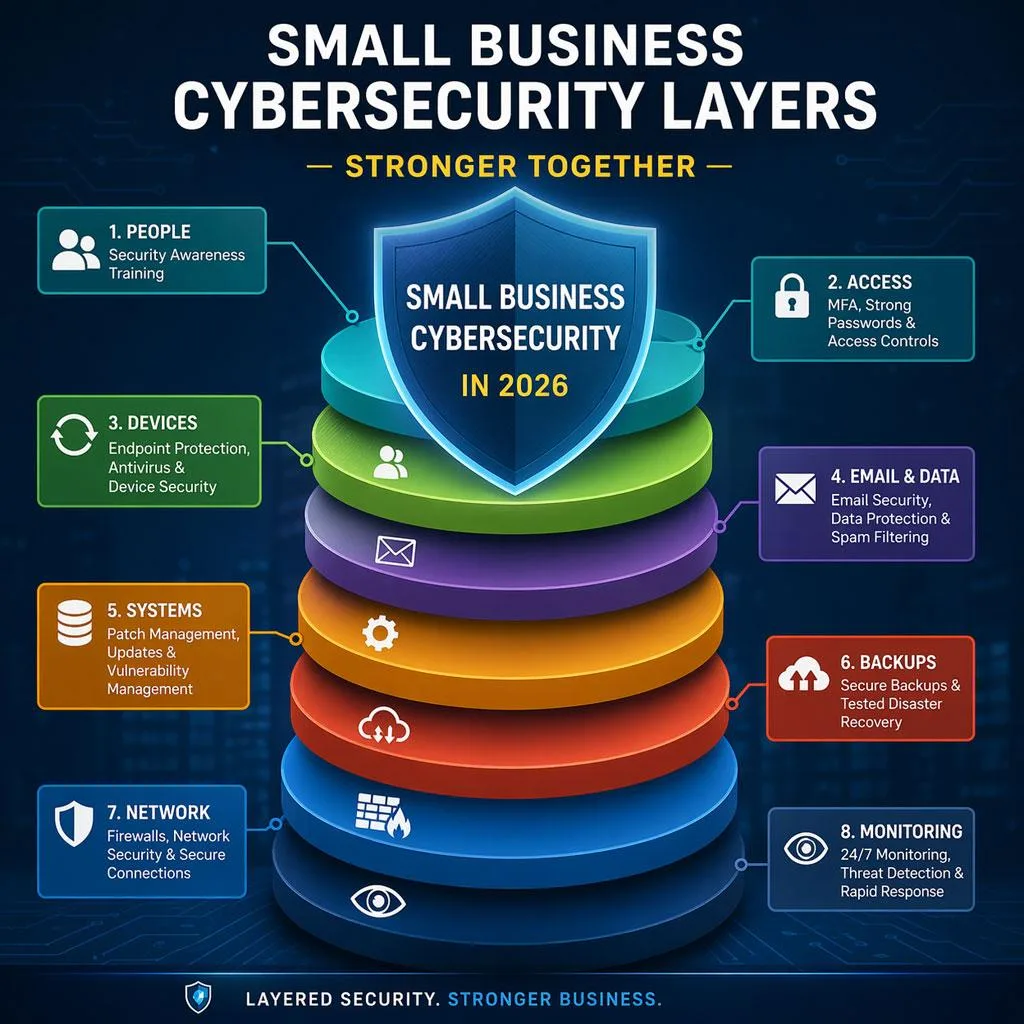
If antivirus is one layer, what are the other layers?
A small business in 2026 should think in terms of defense in depth. That means using several protections together so one failure does not become a full disaster.
1. Multi-factor authentication
If a password gets stolen, MFA can still stop the attacker from getting in. This is one of the simplest and highest-value security controls a small business can enable. CISA repeatedly recommends MFA across its SMB guidance and ransomware resources.
2. Patch management
Every device, operating system, browser, firewall, and business application should be updated regularly. Attackers love old vulnerabilities. The SBA explicitly recommends automatic updates whenever possible.
3. Backup and recovery planning
Backups are only useful if they work when you need them. Businesses should back up critical systems, protect backup access, and test restores. CISA’s ransomware guidance highlights backup strategy as a core control.
4. Employee security awareness
Your team is either your first line of defense or your biggest risk. Basic training on phishing, password hygiene, suspicious links, and approval processes can make a major difference. The SBA directly recommends employee training as a cyber best practice.
5. Email and identity protection
A lot of modern attacks target Microsoft 365, Google Workspace, and other cloud identities. Security today has to include account protection, login monitoring, and secure access controls, not just file scanning.
6. Endpoint monitoring and response
Many businesses now need more than basic antivirus. They need tools and services that look for suspicious behavior, isolate threats, and help respond quickly. This is where managed detection and response, endpoint detection, and continuous monitoring become important.
7. Secure network and access controls
Your firewall, Wi-Fi, remote access tools, and network devices all matter. A single weak point can open the door to a much bigger problem.
8. Business continuity planning
Security is not only about stopping attacks. It is also about staying operational. The U.S. Chamber’s business continuity guidance points out that companies need to assess risk, understand operational impact, and plan for disruptions before they happen.
So what is the real answer?
Is antivirus enough for a small business in 2026?
No. It is necessary, but it is not enough.
Think of antivirus like a lock on your office door. You still want the lock. But if the windows are open, the alarm is off, the passwords are weak, the cameras are down, and nobody has a plan for an emergency, the lock alone will not save you.
That is how modern business security works.
Antivirus is one part of the picture. Businesses now need a broader approach that protects devices, accounts, email, cloud apps, backups, and day-to-day operations.
What this means for small business owners
If you are a business owner, you do not need to become a cybersecurity expert overnight. But you do need to ask better questions.
Instead of asking:
“Do we have antivirus?”
Ask:
- Do we have MFA on critical accounts?
- Are our systems patched and monitored?
- Are our backups protected and tested?
- Do employees know how to spot phishing attempts?
- Can we recover quickly if something goes wrong?
- Who is watching for issues before they turn into downtime?
Those are the questions that lead to smarter IT decisions.
Why many small businesses still rely too heavily on antivirus
There are a few reasons this still happens.
First, antivirus is familiar. Business owners have heard of it for years, so it feels like the standard answer.
Second, some vendors oversimplify security. They sell one product as if it covers every risk.
Third, small businesses are busy. Owners are trying to manage growth, payroll, customer service, and operations. It is easy to assume that if a security product is installed, the problem is solved.
But small-business cybersecurity has changed. The threat environment is more complex, and the consequences of downtime are more serious.
According to Verizon’s 2025 DBIR materials, SMBs are being targeted far more aggressively than many owners assume. That means smaller businesses cannot afford to rely on outdated assumptions about what protection looks like.
What better protection looks like in the real world
For a small business, better protection usually means:
- managed antivirus or endpoint protection
- multi-factor authentication
- secure email and login protections
- patch management
- backup strategy with recovery testing
- staff training
- ongoing monitoring
- a support partner who can respond when something feels off
That does not mean every business needs enterprise-level complexity. It means every business needs the right level of layered security for its size, risk, and goals.
At Zevonix, we believe technology should support growth, not create confusion. Businesses need security that is practical, proactive, and aligned with real operations.
How Zevonix helps small businesses move beyond “just antivirus”
Zevonix helps businesses build a smarter IT foundation by looking at the full picture, not just one tool.
That can include:
- managed IT support
- cybersecurity hardening
- endpoint protection
- Microsoft 365 security improvements
- backup strategy
- user access control
- device and network visibility
- practical guidance that fits your business
The goal is simple: reduce risk, improve stability, and help your team work with confidence.
Final thoughts
Antivirus still has value. It should absolutely be part of your security stack.
But if you are asking whether antivirus alone is enough for a small business in 2026, the answer is clear: it is not.
Small businesses need protection that matches the way people actually work today. That means securing not just computers, but also email, cloud apps, logins, backups, users, and recovery processes.
The businesses that stay safer are usually not the ones with the fanciest tools. They are the ones with the right layers, the right habits, and the right support.
If your business is still relying mostly on antivirus, now is a good time to take a closer look.
Zevonix helps small businesses build smarter, stronger IT with practical cybersecurity and ongoing support that fits the real world.
Frequently Asked Questions
Is antivirus still necessary for a small business?
Yes. Antivirus is still an important layer of protection. It helps block known malware and suspicious files. But it should be combined with other protections like MFA, patching, backups, and employee training.
What is the biggest security risk for small businesses right now?
There is not just one. Common risks include phishing, ransomware, credential theft, weak passwords, unpatched systems, and poor backup readiness. Federal guidance and current breach reporting point to all of these as ongoing concerns.
Can antivirus stop ransomware?
Sometimes it can help detect or block part of a ransomware attack, but it is not enough by itself. Ransomware defense also depends on MFA, patching, backup protection, and incident response planning.
Does Microsoft 365 or Google Workspace make antivirus unnecessary?
No. Cloud platforms still need strong security settings, identity protection, and endpoint protection. Account compromise, phishing, and device-level threats can still impact your business.
What should a small business do first if it only has antivirus today?
Start by enabling MFA, reviewing backups, updating systems, and training employees to spot phishing. Then evaluate whether you have enough visibility and response capability to catch suspicious activity early.
Stay Informed
Want smarter insights without the noise? Get our latest ideas and strategies delivered right to your inbox.
We respect your privacy. Unsubscribe at any time.
